top of page


MY NAME IS,
SAINT MAIDEN

CYBERSECURITY
AND I AM A
ANALYST
My name is Darnell Maiden. I go by Saint, and this is my story on how I jumped into a
career in cybersecurity. On January 21st, 2026, I sit at my desk in frustration over two pizza jobs I wanted to quit. With 14 years of customer service jobs and food related positions, I felt stuck. I didn't have any special career skills that would get me further in life and making pizzas wasn't going to get me the life I wanted. After a long sigh and a long stare at my laptop, I searched for careers that would interest me. I was taken to a survey site, where I was asked a bunch of intricate questions about what I wanted to do in life. After watching the spinner icon move for 2 minutes, my results came back. It said... Cybersecurity.
THE STORY
"CYBERSECURITY? LIKE THE MATRIX?"
Clearly I was extremely clueless on this, so I did extensive research. For the first time in my life, I was actually excited about something. I've always been interested in technology, but this? This was a new opportunity to be of service to the world. I could fight all the cybercrime, protect people, and do it while looking good too? Pfft. Sign me up. I loved the idea and concept behind me being in cybersecurity. It felt official, cool, and a pretty awesome occupation title. There was only one thing that bugged my mind after my amazing visualizations...
"WHERE DO I START?"
A couple searches later and boom. The "Google Cybersecurity Professional Certificate" link appeared before me. I was nervous. What if it's way too hard? What if I don't get it in time? What if... shut up. I killed every "what if" that night and buried it with my doubts and disbeliefs within myself. I enrolled in a program that would take 6 months to complete... I got it done in 2 months and a week. March 6th, 2026 to be exact. Do you want to know what happened weeks later? On March 21st, 2026, I got my CompTIA Security+ certification. Tears of joy? More like running around the room like a damn maniac screaming "LET'S GOOOOOO!" multiple times. Yeah, I was happy. Now, after celebrating with too much Little Cesar's Pizza and finally relaxing, I said the grand question that brought me here today....
"SO WHAT'S NEXT?"
Well, before I get into that, I want to tell you why I got into cybersecurity. I got into this field because of the versatility. The challenges that evolve themselves as technology evolves as well. I love the fact that I can learn more everyday and never get bored. I can even put my expertise into different domains like cloud security and network security. I love how complex it is. It's like a Rubix Cube with more colors and combinations that change everyday, you can twist the image anyway you want to, but there's always another picture to discover on the other side of that image. That is why I love cybersecurity. For it's ever evolving challenge and the spread of knowledge that I can gain from it. But, I know what you're still asking....
"HEY SAINT, WHAT'S NEXT?"
Honestly, what's next in life is A job in a SOC, cloud security, a few degrees in Computer Science, more certifications in specialized tools and domains, and possibly a move to the west coast to expand more in the tech scene. I look forward to what's coming next and the paths I'll cross. I also want to be a full-stack software developer, front-end and back-end. This is my life now. I am in the seat of the Lamborghini we call Cybersecurity, cruising through the beautiful road we call life and making my mark on these pretty streets called history. This is something I will forever be dedicated to along with many other things. If you're reading this and got all the way here, shoot me an email and let's connect. I might be a ghost at times but I'm always willing to give you a piece of my spirit too. My final word to end all of this is...
"DON'T BE COMFORTABLE, BE GREATER. FORTIS/FORTUNA/ADIUVAT."
- SAINT MAIDEN
PROJECTS
.png)
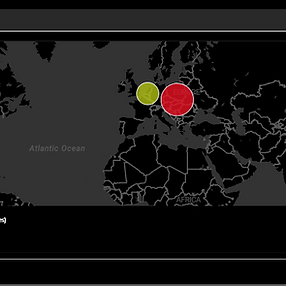
SOC LAB & SIEM W/ MICROSOFT SENTINEL IN AZURE
Architected and deployed a cloud-native SIEM environment using Microsoft Sentinel and Azure Log Analytics. Configured a honeypot virtual machine to capture RDP brute-force attacks, utilizing PowerShell to extract geolocation data and visualize global threat actors via a live Sentinel Map.

VULNERABILITY SCANNER DEPLOYMENT W/ NESSUS
Utilized Nessus Essentials to manage the full vulnerability lifecycle for a Log4j-vulnerable Minecraft server. Conducted credentialed scans to identify high-risk gaps and prioritized remediation using CVSS scores for CVE-2021-44228. Executed targeted patching and system hardening, achieving 100% resolution of all critical findings as verified by follow-up audits.
.png)
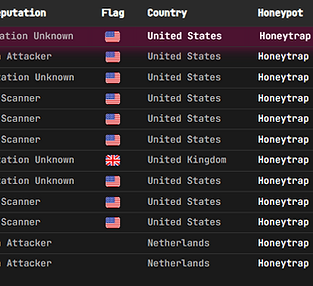
T-POT HONEYPOT LAB W/ DIGITAL OCEAN
Deployed a T-Pot honeypot framework on DigitalOcean to monitor global adversary behavior. I utilized the ELK Stack to aggregate and visualize real-time threat intelligence from multiple vectors, including SSH and HTTP exploits. This setup allowed for the identification of malicious IP patterns and live tracking of brute-force attempts across diverse geographical regions.
PASSWORD MGMT SYSTEM W/ AWS & PASSBOLT
Deployed a secure Passbolt password management solution on AWS to centralize and protect sensitive credentials. I configured the cloud infrastructure to ensure end-to-end encryption, robust access controls, and high availability, focusing on security best practices for organizational data management.
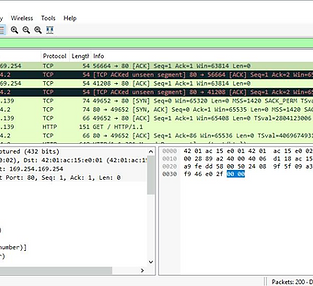
ANALYZING PACKETS W/ WIRESHARK
Conducted deep-packet analysis using Wireshark to intercept and examine live network traffic. I utilized various display filters to isolate specific protocols, such as TCP, HTTP, and DNS, and performed stream reassembly to reconstruct session data. This project focused on identifying suspicious patterns, analyzing three-way handshakes, and understanding the flow of unencrypted data within a network environment.
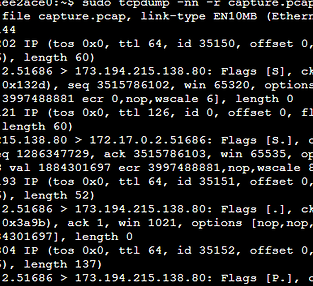
CAPTURING PACKETS W/ TCPDUMP
Utilized tcpdump via the command line to capture and filter live network traffic on a Linux interface. I performed targeted packet captures, analyzed headers to troubleshoot connectivity, and exported data to .pcap files for deep inspection, mastering CLI-based traffic analysis at the packet level.
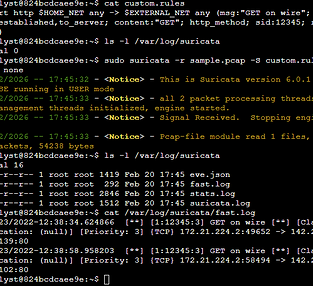
EXAMINING RULES, ALERTS & LOGS W/ SURICATA
Deployed Suricata as a Network Intrusion Detection System (NIDS) to monitor and analyze network traffic for malicious activity. I authored and implemented custom intrusion detection rules to trigger alerts upon identifying specific threat patterns, such as unauthorized access attempts and protocol anomalies. This project involved deep-dive log analysis of Eve.json outputs to refine alert accuracy and strengthen network perimeter defense.
SKILLS
SOFT SKILLS:
COMMUNICATION
MULTI-TASKING
CONFLICT DE-ESCALATION
TIME MANAGEMENT
SENSE OF URGENCY
ACCOUNTABILITY
ADAPTIVE PROBLEM SOLVING
COMPOSURE (STRESS TOLERANCE)
EMOTIONAL INTELLIGENCE
TECH SKILLS:
KQL (KUSTO QUERY LANGUAGE)
MICROSOFT SENTINEL
LOG ANALYTICS
SIEM TOOLS (WAZUH, ELK, SENTINEL)
VULNERABILITY SCANNING (NESSUS)
PACKET ANALYSIS (WIRESHARK/TCPDUMP)
THREAT DETECTION (THREAT MAPPING, T-POT)
CLOUD CONFIGURATIONS (AZURE, AWS, DIGITAL OCEAN)
CLI (LINUX, POWERSHELL, BASH, SQL)
FRAMEWORKS (NIST CSF, INCIDENT RESPONSE LIFECYCLE, RMF)
VIRTUALIZATION (VIRTUAL BOX, UBUNTU, KALI LINUX, WINDOWS SERVER)
ACTIVE DIRECTORY
CERTIFICATIONS
GOOGLE CYBERSECURITY

DATE OBTAINED: MAR 6TH, 2026
ISSUED BY: COURSERA
COMPTIA SECURITY+ CE
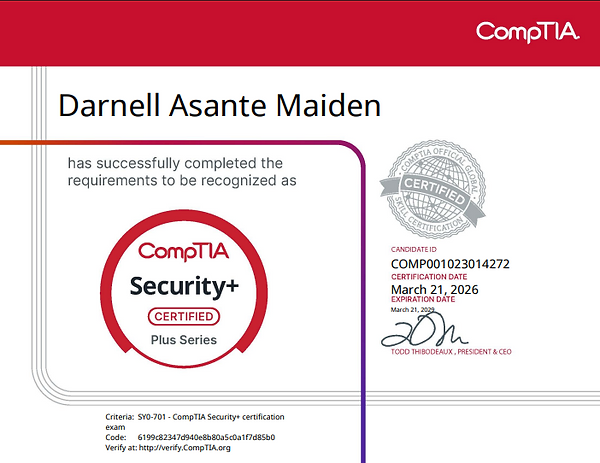
DATE OBTAINED: MAR 21ST, 2026
ISSUED BY: COMPTIA
MORE COMING SOON.
bottom of page