PASSWORD MANAGER HOSTED IN THE CLOUD
A PROJECT BY DARNELL MAIDEN
INTRODUCTION:
IN THE MODERN THREAT LANDSCAPE, IDENTITY IS THE NEW PERIMETER. WHILE ROBUST FIREWALLS AND SOPHISTICATED ENCRYPTION PROVIDE A STRONG FOUNDATION, THE SECURITY OF AN ENTIRE NETWORK OFTEN HINGES ON THE STRENGTH AND MANAGEMENT OF INDIVIDUAL USER CREDENTIALS. THIS LAB EXPLORES THE FUNDAMENTAL SHIFT FROM TRADITIONAL, EASILY EXPLOITABLE PASSWORD HABITS TO A ZERO TRUST APPROACH TO IDENTITY MANAGEMENT.
THE OBJECTIVE OF THIS PROJECT IS TO SIMULATE A SECURE CREDENTIAL LIFECYCLE. BY DEPLOYING A CENTRALIZED PASSWORD MANAGEMENT SOLUTION, WE ADDRESS THE CRITICAL RISKS ASSOCIATED WITH PASSWORD REUSE, CREDENTIAL STUFFING, AND THE STORAGE OF SENSITIVE DATA IN UNENCRYPTED FORMATS.
THE PROBLEM:
THE RELIANCE OF PASSWORD MEMORIZATION HAS BEEN A MAJOR VULNERABILITY FOR YEARS. USERS OFTEN REUSE WEAK CREDENTIALS WHICH IN RESULT, CREATES A MASSIVE ATTACK SURFACE. ONE BREACH CAN LEAD TO MULTIPLE CREDENTIALFF STUFFING ATTACKS, GRANTING UNAUTHORIZED ACCESS TO SENSITIVE ACCOUNTS. WITHOUT SECURE GENERATION AND STORAGE, THE HUMAN ELEMENT REMAINS THE WEAKEST LINK IN THE SECURITY CHAIN.
THE SOLUTION:
THIS LAB DEMONSTRATES AN OPEN SOURCE PASSWORD MANAGEMENT ECOSYSTEM UTILIZING PASSBOLT DEPLOYED WITHIN THE AWS CLOUD ENVIRONMENT. BY LEVERAGING CLOUD INFRASTRUCTURE, THE SOLUTION ENSURES HIGH AVAILABILITY AND SCALABILITY WHILE MAINTAINING RIGOROUS SECURITY STANDARDS.
TECH STACK
AWS CLOUD SERVICES
PASSBOLT
KALI LINUX VM
BEFORE I DO ANYTHING TOO TECHNICAL, I'LL OPEN UP MY AWS ACCOUNT

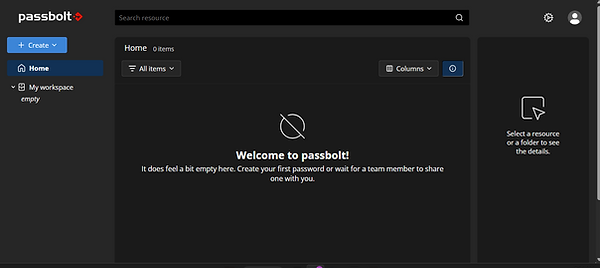
THIS IS PASSBOLT. OUR STORAGE. THE STORNGHOLD. THE SOURCE. LOOK, YOU GET IT. LET'S GET STARTED WITH A PREM-INSTALL.


LET'S HEAD TO THE COMMUNITY SECTION. WHY? I'M BROKE THAT'S WHY.
(RECRUITERS, HOLLA @ ME).
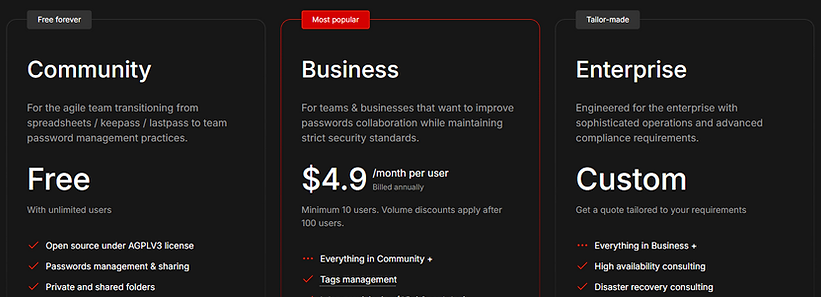
I'LL USE AWS FOR DEPLOYMENT.


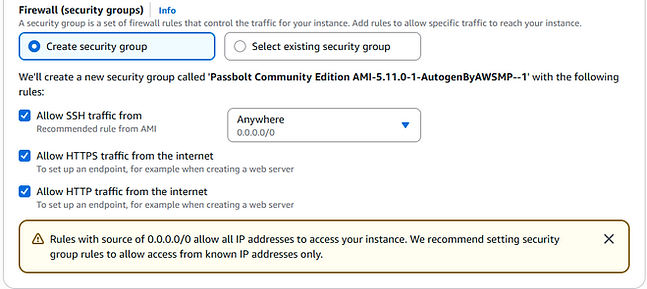
AFTER GOING TO THROUGH PURCHASING, CONFIGURATION, AND LAUNCH OPTIONS I HEADED TO THE SECURITY GROUPS. I OPENED UP PORT 22 SSH ALONG WITH HTTP AND HTTPS.

NEXT, I CREATED A KEY PAIR. THIS IS USED TO SECURELY CONNECT TO AMAZON ELASTIC COMPUTE CLOUD. WHEN YOU LAUNCH AN EC2 INSTANCE, YOU MIGHT SPECIFY A KEY PAIR FOR THE INSTANCE. IT CONSISTS OF A PUBLIC KEY AND PRIVATE KEY WHICH ARE USED TO SECURELY AUTHENTICATE THE ACCESS TO MY INSTANCE.


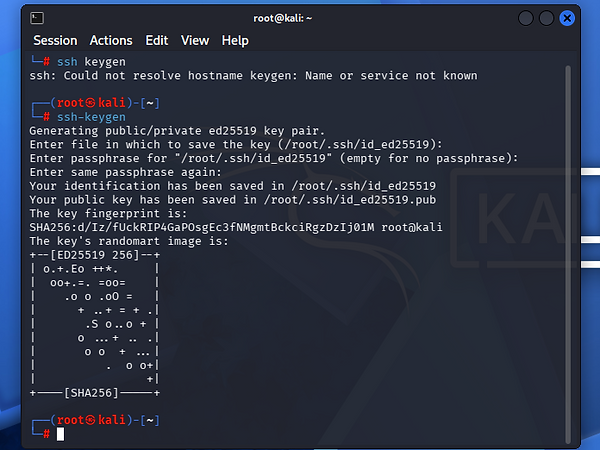
TIME TO IMPORT MY KEY PAIR. LET'S FIRE UP KALI LINUX.
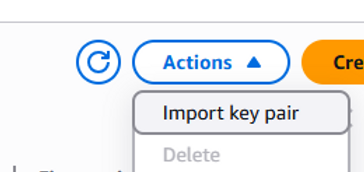
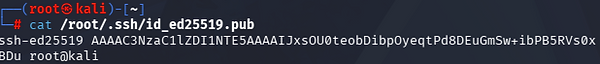
I HOPPED ON MY KALI LINUX MACHINE, GENERATED A KEYPAIR VIA SSH-KEYGEN, RETRIEVED THE PUBLIC KEY WITH CAT, AND PASTED THE OUTPUT DIRECTLY INTO THE AWS EC2 "IMPORT KEY PAIR" FIELD.

AFTER CONFIGURING MY NETWORK SETTINGS, I LAUNCHED MY INSTANCE AND SEEN THE SUCCESS. I HAD TO CHANGE THE HOST ADDRESS OF MY INSTANCE TO "HTTPS" AND "HTTP". LET'S BEGIN.

I'M HOSTING THIS IN THE CLOUD SINCE I DON'T HAVE A DOMAIN NAME FOR THE SSL OPTION. I STARTED THE CONFIGURATION AND KEPT THE DATABASE DEFAULTS THE SAME.

I WENT TO THE "SERVER KEYS" SECTION AND FILLED OUT THE SERVER NAME, EMAIL, AND KEY TYPE/KEY LENGTH.

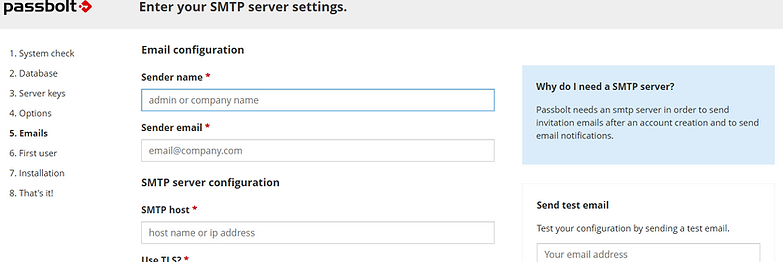
NOW SINCE I'M IN THE SMTP, I WANT TO MAKE A SMALL DISCLAIMER. SINCE THIS IS NOT GOING TO BE A PERMANENT PASSWORD MANAGER, I DON'T HAVE TO FILL OUT ALL THE SMTP INFORMATION. I'LL STILL FILL OUT THE EMAIL CONFIGURATION.
LET'S CREATE OUR USER ACCOUNT NOW.

MY INSTALLATION IS COMPLETE NOW AND I'LL INSTALL THE CHROME EXTENSION.


I CREATED A PASSPHRASE, DOWNLOADED MY RECOVERY KIT, AND PICKED A COLOR PLUS 3 THREE CHARACTERS




AND BOOM! I MADE A PASSWORD MANAGER! YOU CAN CREATE PASSWORDS, NOTES, ETC. THIS PROVIDED PROVISIONING INFRASTRUCTURE BY DEPLOYING A VIRTUAL MACHINE IN THE CLOUD, GAVE AUTHENTICATION BY USING SSH KEY PAIRS TO SECURELY CONNECT TO THE HOST, AND IT ELIMINATES WEAK HABITS FROM PASSWORD REUSE AND CREDENTIAL STUFFING BY GENERATING AND STORING COMPLEX, UNIQUE PASSWORDS FOR EVERY SERVICE.
CONCLUSION:
BY DEPLOYING A PASSBOLT INSTANCE WITHIN THE AWS CLOUD, THIS LAB SUCCESSFULLY DEMONSTRATES THE TRANSITION FROM VULNERABLE, MEMORY-BASED CREDENTIAL HABITS TO A ROBUST ZERO TRUST IDENTITY MANAGEMENT STRATEGY. THROUGH THE INTEGRATION OF KALI LINUX FOR SECURE KEY GENERATION AND EC2 INFRASTRUCTURE FOR SCALABLE HOSTING, WE HAVE CREATED A CENTRALIZED "STRONGHOLD" THAT ENSURES DATA SOVEREIGNTY AND END-TO-END ENCRYPTION. THIS ECOSYSTEM NOT ONLY ELIMINATES THE RISKS OF CREDENTIAL STUFFING AND PASSWORD REUSE BUT ALSO PROVIDES A SEAMLESS, TEAM-ORIENTED WORKFLOW FOR MANAGING THE MODERN ATTACK SURFACE. ULTIMATELY, THIS PROJECT PROVES THAT LEVERAGING OPEN-SOURCE TOOLS IN THE CLOUD CAN EFFECTIVELY MITIGATE THE HUMAN ELEMENT AS THE WEAKEST LINK IN THE SECURITY CHAIN.