top of page
MICROSOFT AZURE/SENTINEL SOC LAB
.png)
A PROJECT BY DARNELL MAIDEN
INTRODUCTION
EFFECTIVE THREAT DETECTION REQUIRES MORE THAN JUST LOG COLLECTION; IT REQUIRES CONTEXT. THIS LAB DEMONSTRATES A COMPLETE SOC (SECURITY OPERATIONS CENTER) WORKFLOW. USING MICROSOFT SENTINEL AND LOG ANALYTICS, I CONFIGURED A SYSTEM TO INGEST SECURITY EVENTS FROM A WINDOWS VM. I THEN DEVELOPED A CUSTOM POWERSHELL SCRIPT TO QUERY A THIRD-PARTY API FOR GEOGRAPHIC DATA, ALLOWING ME TO MAP MALICIOUS IP ADDRESSES. THE RESULT IS A DYNAMIC DASHBOARD THAT PROVIDES IMMEDIATE VISUAL INSIGHT INTO THE PERSISTENT NATURE OF GLOBAL CYBER-RECONNAISSANCE.
THE PROBLEM:
MANY ORGANIZATIONS DEPLOY CLOUD INFRASTRUCTURE WITHOUT ADEQUATE MONITORING, LEAVING THEM VULNERABLE TO AUTOMATED BOTS THAT CONSTANTLY SCAN THE INTERNET FOR OPEN RDP PORTS. WITHOUT A PROPER SIEM (SECURITY INFORMATION AND EVENT MANAGEMENT) SYSTEM, SECURITY ANALYSTS ARE OFTEN BURIED IN RAW LOG DATA THAT LACKS GEOGRAPHIC CONTEXT, MAKING IT IMPOSSIBLE TO IDENTIFY WHERE ATTACKS ARE ORIGINATING OR TO RECOGNIZE PATTERNS IN MALICIOUS ACTIVITY BEFORE A BREACH OCCURS.
THE SOLUTION:
TO ADDRESS THIS, I ARCHITECTED A SOC LAB WITHIN MICROSOFT AZURE THAT AUTOMATES THE LOG INGESTION AND VISUALIZATION PROCESS. BY EXPOSING A WINDOWS VM (HONEYPOT) TO THE OPEN INTERNET, I USED LOG ANALYTICS WORKSPACES TO CAPTURE FAILED RDP LOGINS. I AUTHORED CUSTOM KQL (KUSTO QUERY LANGUAGE) QUERIES TO EXTRACT IP METADATA AND INTEGRATED A GEOLOCATION API VIA POWERSHELL TO ENRICH THE DATA. FINALLY, I MAPPED THIS DATA WITHIN MICROSOFT SENTINEL, TRANSFORMING THOUSANDS OF RAW LOGS INTO A LIVE ATTACK MAP THAT PROVIDES INSTANT, ACTIONABLE THREAT INTELLIGENCE.
TECH STACK
HOST OS
MICROSOFT AZURE
MICROSOFT SENTINEL
AZURE VM
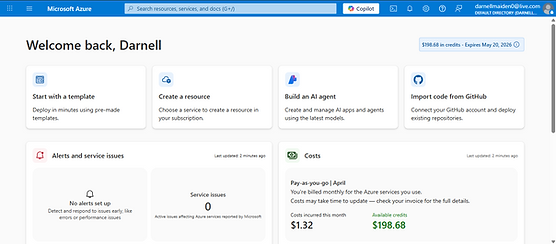
FOR OBVIOUS REASONS, I CREATED AN AZURE ACCOUNT WITH A SUBSCRIPTION.

ONCE MY ACCOUNT WAS SETUP, I SKIPPED THE QUICK START AND GOT TO WORK.
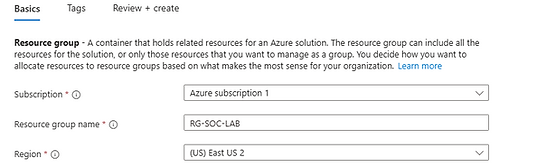
I STARTED OFF BY CREATING A RESOURCE GROUP WHICH IS A LOGICAL CONTAINER IN AZURE THAT HOLDS ALL RELATED RESOURCES FOR AN ARCHITECTUAL SOLUTION. I'LL CREATE THE BASICS FOR IT SUCH AS THE VIRTUAL NETWORK AND THE VIRTUAL MACHINE. LET'S CONFIGURE THE RESOURCE GROUP FIRST.
.png)

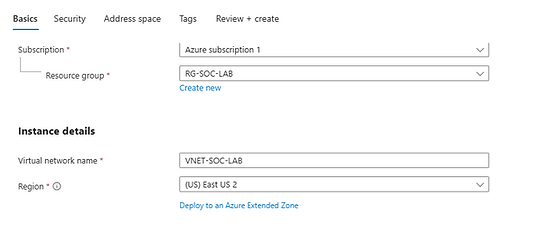
NOW LET'S GET THE VIRTUAL NETWORK GOING. I KEPT EVERYTHING ELSE AT DEFAULT TO KEEP IT SIMPLE. THE VIRTUAL NETWORK WILL PROVIDE US OUR PUBLIC IPV4 AND PRIVATE IPV4 AS WELL, WHICH IS GOING TO BE VERY ESSENTIAL IN REMOTE LOGINS.
.png)
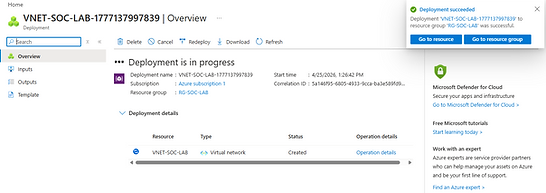
NOW WE WILL CREATE THE VIRTUAL MACHINE. THE VIRTUAL MACHINE WILL BE OUR TARGET, THE CRASH DUMMY, THE TEST SUBJECT. YOU GET THE DRIFT. WE WILL USE THIS FOR LOG COLLECTIONS AND ATTACKER ANALYSIS AS WELL. VIRTUAL MACHINES CAN BE USED FOR ANYTHING OTHER THAN ANALYSIS. IT CAN BE USED TO IDENTIFY MALICIOUS FILES OR JUST HOSTING A SANDBOX ENVIRONMENT TO WRECK THINGS IN. ALL IN ALL, VIRTUAL MACHINES GIVE US THE ABILITY TO TEST AND ANALYZE WITHOUT RUINING OUR OWN MACHINE.
.png)
.png)
IN THE CONFIGURATION PROCESS, I STARTED BY CHOOSING MY NAME, THE RESOURCE GROUP IT BELONGED TO, THE MACHINE IMAGE (WINDOWS 10 ENTERPRISE) ALONG WITH THE SIZE, LOCATION, CREDENTIALS, AND THE VIRTUAL NETWORK I WANTED TO CONNECT TO IT AS WELL. NOW I HAVE TO CONFIGURE THE NETWORK SECURITY GROUPS.
THIS IS THE NETWORK SECURITY GROUP SECTION. THE INBOUND RULES CONTROL WHAT TRAFFIC CAN ENTER THE VIRTUAL NETWORK FROM THE PUBLIC INTERNET.
.png)
I DID TWO THINGS WITH THIS CONFIGURATION. FIRST, I DELETED THE RDP RULE TO MAKE MY MACHINE AS ENTICING AS POSSIBLE. LASTLY, I CREATED A NEW INBOUND RULE THAT ALLOWED ALL SOURCE PORT RANGES AND ALL DESTINATION POINT RANGES BY USING ( * ). THAT WAY, ATTACKERS SEE A WELCOME MAT TO MY VM AND BECOME A PIECE OF TEST DATA I WILL USE LATER ON IN THIS PROJECT.
NOW THAT THE NETWORK SECURITY GROUPS ARE CONFIGURED, LET'S LOG INTO THE VM USING A REMOTE DESKTOP CONNECTION THAT WAS ALREADY INSTALLED ON MY WINDOWS OS. I ENTERED MY VM CREDENTIALS AND IP ADDRESS AND WENT THROUGH MY WINDOWS VM SETUP.
_edited.jpg)
AGAIN, WE WANT TO MAKE THIS AS ENTICING AS POSSIBLE. SO LET'S GET RID OF THAT VM FIREWALL, SHALL WE? NEXT, I NEED TO MAKE SURE THE CONNECTION TO THE VM IS ACTIVE, SO I'LL PING MY VM IP FROM MY WINDOWS OS. AS YOU CAN SEE, THAT WAS A SUCCESS. SO IF IT'S A SUCCESS FOR ME, THAT MEANS THE ATTACKERS HAVE THEIR DOORMAT, THE THING IS, THE DOOR NEVER OPENS. IT ONLY TRACKS, LOGS, AND MAKES YOU LOOK STUPID IN THE PROCESS. KNOCK, KNOCK.
.png)
_edited.jpg)
AFTER LOGGING OUT, I DECIDED TO DO SOME LOGIN FAILURES ON MY OWN VM ON PURPOSE TO TRIGGER SOME ACTIVITY. THIS IS IMPORTANT FOR WHAT I'M ABOUT TO SHOW IN THE NEXT STEP.
LET'S EXPLORE THE EVENT VIEWER IN OUR WINDOWS VM. THIS IS WHERE ALL THE SECURITY EVENTS ARE FROM THE LOGIN ATTEMPTS TO LOGIN FAILURES. IF YOU CLICK ON EVENT TWICE, THE SEARCH BAR WILL APPEAR. I USE THIS TO HELP ME FIND SPECIFIC EVENTS USING EVENT ID NUMBERS. IF I WANTED TO SEE MORE INFORMATION ON AN EVENT, I'D CLICK ON IT TWICE AND PULL IT DOWN TO SEE MORE INFORMATION, LIKE ACCOUNT NAMES, IP ADDRESS, ETC. YOU CAN ALSO FILTER CURRENT LOGS ON THE RIGHT TO FILTER FOR EXACT INFORMATION AND REMOVE OTHER LOGS THAT DON'T CORRESPOND TO THE SEARCH QUERY. THIS IS WHY I CREATED THOSE FAILED LOGINS, TO DISPLAY THE POWER OF THE EVENT VIEWER.
.png)
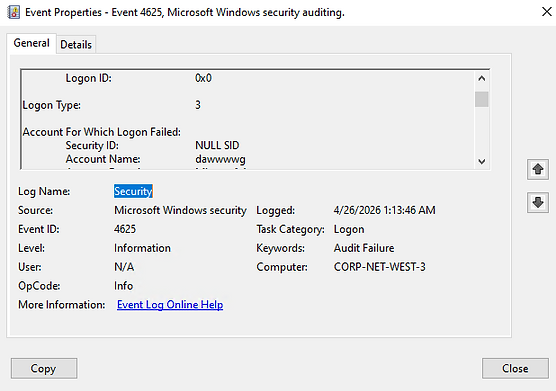.png)
.png)
.png)
AFTER LOGGING OUT OF MY VM, I WENT BACK TO THE AZURE PORTAL TO CONFIGURE MY LOG ANALYTICS WORKSPACE, WHICH IS THE CENTRAL DATA REPOSITORY IN AZURE WHERE LOG DATA FROM VARIOUS SOURCES IS COLLECTED, AGGREGATED, AND STORED. IT ACTS AS THE "BRAIN" OF YOUR MONITORING SETUP, PROVIDING THE SEARCH AND ANALYTICS CAPABILITIES (VIA KQL) THAT ALLOW MICROSOFT SENTINEL TO IDENTIFY SECURITY THREATS. I CONFIGURED THE RESOURCE GROUP SELECTION, THE NAME, AND REGION AS WELL.
.png)
NOW IT'S TIME TO CREATE THE SENTINEL. MICROSOFT SENTINEL IS A CLOUD-BASED SIEM (SECURITY INFORMATION AND EVENT MANAGEMENT) AND SOAR (SECURITY ORCHESTRATION, AUTOMATION, AND RESPONSE SOLUTION. IT AGGREGATES DATA FROM THE LOG ANALYTICS WORKSPACE TO DETECT. INVESTIGATE, AND RESPOND TO THREATS ACROSS MY DIGITAL REALM IN AZURE.
.png)
I WILL LINK MY ANALYTICS WORKSPACE TO THE SENTINEL SO IT CAN COLLECT LOGS AND DATA FROM IT. IN ORDER TO DO THAT, I MUST CREATE A CONNECTION BETWEEN THE LOG ANALYTICS WORKSPACE AND THE VM SO I CAN RECIEVE THE LOGS IN SENTINEL AND OBSERVE THEM. TO DO THAT, I WILL CONFIGURE THE AZURE MONITORING AGENT SECURITY EVENT CONNECTOR BY INSTALLING WINDOWS SECURITY EVENTS.
NOW I HAVE TO CONFIGURE THE AZURE MONITORING AGENT SECURITY EVENT CONNECTOR, THIS WILL CREATE A CONNECTION BETWEEN THE LOG ANALYTICS WORKSPACE AND THE VM SO WE CAN RECIEVE THE LOGS FROM THE SENTINEL AND OBSERVE THEM. I'LL GET A DOWNLOARD FROM TCONTENT HUB OF THE WINDOWS SECURITY EVENTS, WHICH IS A DATA CONNECTOR WITHIN THE MICROSOFT SENTINEL THAT STREAMS SECURITY LOGS FROM MY WINDOWS VIRTUAL MACHINES INTO MY LOG ANALYTICS WORKSPACE. IT'LL DOWNLOAD IN THE BACKGROUND. I'LL CHECK ON IT IN A FEW.
.png)
.png)
NOW, AFTER DOWNLOADING THE WINDOWS SECURITY EVENTS VIA AMA, I CLICKED ON THE CONNECTOR PAGE AND CREATED A DATA COLLECTION RULE THAT IS USED TO FORWARD LOGS INTO MY LOG ANALYTICS WORKSPACE WHICH LETS ME ACCESS THE INSIDE OF THE SIEM. I MADE A NAME FOR THE RULE, CHOSE MY RESOURCE GROUP, CLICKED ALL 3 SECTIONS IN MY AZURE SUBSCRIPTION, TOLD IT TO COLLECT ALL LOGS, AND CLICKED CREATE.
.png)
.png)

.png)
AFTER A FEW MINUTES, MY AZURE MONITORING AGENT EXTENSION IS FINALLY INSTALLED. AS A REFRESHER, THE AZURE MONITORING AGENT EXTENSION IS IS A CRITICAL COMPONENT FOR GATHERING DATA FROM THE VIRTUAL MACHINES.
.png)
NOW I'M IN THE LOG ANALYTICS WORKPLACE SECTION. I'M STARTING TO PICK UP TRAFFIC FROM A FEW SOURCES. IT'S GETTING HECTIC NOW. THIS IS WHAT WE WANT. THE DATA BELOW IS PUT INTO A PRETTY FORMAT CALLED A "TABLE". IT'S JUST A FANCY SPREADSHEET OF DATA STATISTICS THAT CAN BE USED TO PINPOINT CORRESPONDING EVENTS. SINCE THE AMA IS FORWARDING THE LOGS INTO THE L.A.W., YOU CAN QUERY SPECIFIC COMPONENTS OF THAT DATA SUCH AS USERNAME, IP, ETC. LET ME SHOW YOU A FEW EXAMPLES.
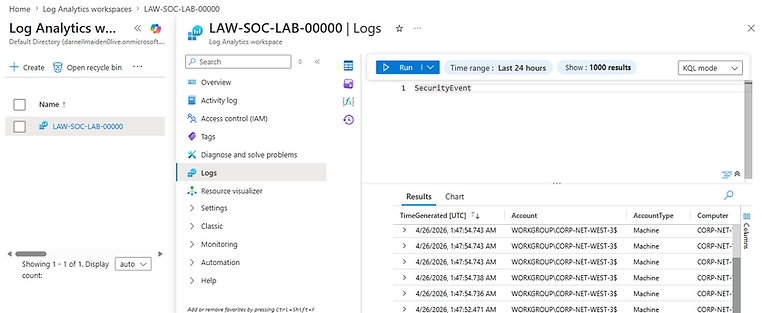.png)
FOR EXAMPLE, IF I ONLY TO SEE THE LOGS WHERE ACTIVITY WAS PERFORMED BY A SPECIFIC USER, IN THE TIME SPAN OF 24 HOURS WITH SPECIFIED COLUMNS, THE QUERY WOULD LOOK LIKE THIS.

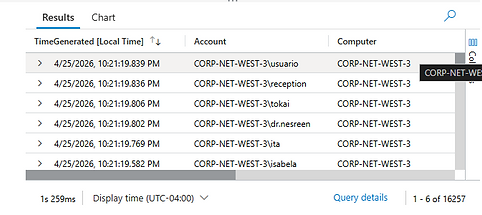
AND IF I WANTED TO SEE THE FAILED LOGINS WITH THE EVENTID "4625" WITHIN THE SPAN OF 24 HOURS WITH THE PROJECT OPERATOR DISPLAYING SPECIFIED COLUMNS IT WOULD LOOK LIKE THIS.
.png)
ALSO, IT'S STARTING TO GET WICKED IN THESE LOGS, THIS IS WHAT HAPPENED AFTER AN HOUR.

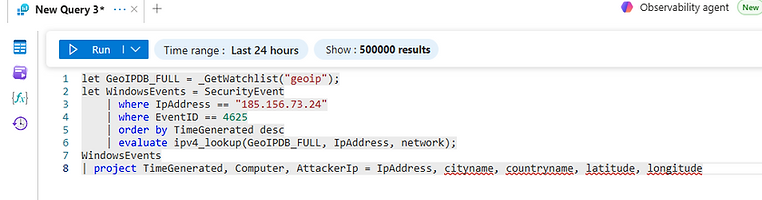
NOW WOULDN'T IT BE NICE TO HAVE GEOGRAPHICAL LOCATIONS NEXT TO OUR EVENTS? PINPOINTS THAT WE CAN PLACE ON A MAP TO FIGURE OUT WHERE MALICIOUS TRAFFIC IS COMING FROM? OF COURSE. I'LL START BY UPLOADING A SPREADSHEET FULL OF LOCATIONS AND COMMON IP ADDRESSES AND UPLOAD IT TO A SENTINEL WATCHLIST. ONCE I DO THIS, IT WILL CREATE ANOTHER TABLE IN THE LOG ANALYTICS WORKSPACE.
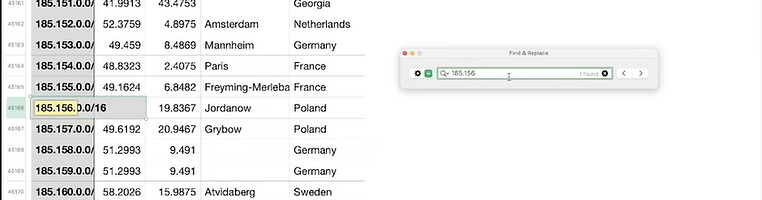.png)
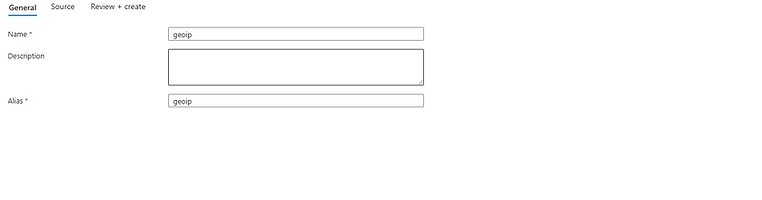.png)
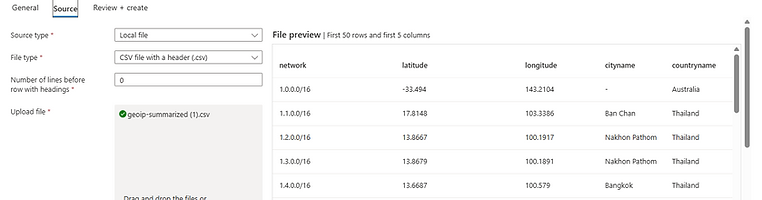.png)
.png)
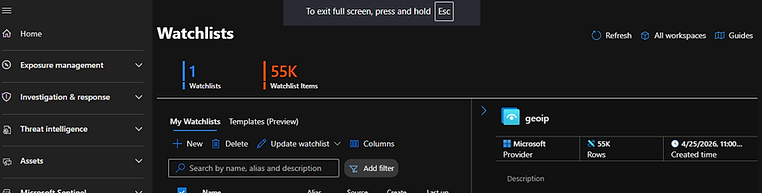
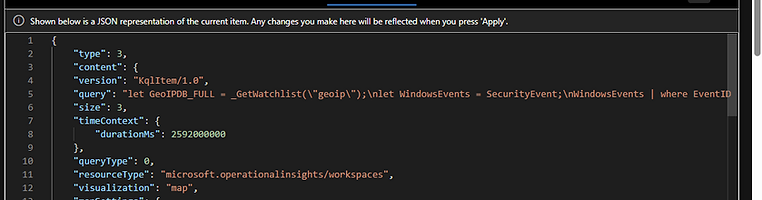
IF YOU TYPE OUT THIS QUERY...
.png)
EVERY FIELD FROM THE WATCHLIST WILL BE UPLOADED AND CREATED INTO IT'S OWN TABLE SUCH AS CITY NAME, COUNTRY NAME, LATTITUDE, AND LONGITUDE. THESE WILL BE IMPORTANT FOR OUR ATTACK MAP.
.png)
IF I TYPE IN THIS QUERY, THIS WILL GIVE ME FULL ACCESS TO THE WATCHLIST DATA WHICH CONTAINS LOCATIONAL DATA WHILE PINPOINTING FAILED LOGIN ATTEMPTS OF A SPECIFIC ATTACKER IP IN A DESCENDED TIME GENERATED ORDER. I CAN ALSO PROJECT CERTAIN FIELDS TO NARROW DOWN THE INFORMATION AS WELL.
.png)
NOW IT'S TIME TO MAKE AN ATTACK MAP. I WENT BACK TO MY SENTINEL INSTANCE AND WENT TO THE WORKBOOKS SECTION IN THREAT MANAGEMENT. I COPIED AN ATTACK MAP JSON CODE AND PASTED IT IN THE ADVANCED EDITOR SECTION. I ALSO CONNECTED THIS TO MY RESOURCE GROUP AS WELL. THIS WILL ALLOW ME TO CONNECT TO THE DATA IN THE LOG ANALYTICS AND TRANSMIT IT TO MY ATTACK MAP. AFTER I CONFIGURED IT, I CLICKED SAVE AND I WAS DONE. VOILA. MISSION ACCOMPLISHED.
.png)
.png)
.png)
TO BREAK THIS QUERY DOWN SIMPLY...
THIS QUERY BASICALLY SAYS:
"FIND ALL FAILED LOGINS, LOOK UP WHERE THEY CAME FROM ON THE MAP, COUNT HOW MANY TIMES EACH LOCATION ATTACKED US, AND CLEAN UP THE LABELS FOR THE DASHBOARD".
.png)
AFTER WAITING OR ABOUT AN HOUR. THIS WAS MY ATTACK MAP. I HAD AN ATTACK MAP RESULT AFTER 24 HOURS BUT MY COMPUTER CORRUPTED THE FILE. I WAS VERY SAD BUT JUST KNOW, THAILAND, THE NETHERLANDS, GERMANY, AND POLAND WE'RE IN THE 100K RANGE. IN RESULT, I SET UP A VULNERABLE VM THAT ATTRACTED ATTACKERS FROM THE PUBLIC INTERNET, LURED THEM AS DATA FOR THE LOGS, CONNECTED THE VM TO MY LOG ANAYLTICS WORKSPACE, AND USED THAT DATA TO FEED INTO AN ATTACK MAP THAT PINPOINTED LOCATIONAL DATA. COOL RIGHT? I THOUGHT SO.
.png)
CONCLUSION
WELL, OUR SENTINEL JOURNEY ENDS HERE BUT, I HAD A LOT OF FUN. I CONFIGURED A LAB THAT TRANSFORMED RAW, CRYPTIC LOGS INTO GEOGRAPHICAL DATA AND FOUND ANOMALIES ALL OVER THE WORLD AND WE BUILT IT ALL FROM AZURE. THIS MAY HAVE NOT BEEN AN ALL OUT SIEM LAB, BUT IT'S A PEEK INTO THE GEOGRAPHICAL ATTACK SURFACE AND AN OUTLOOK AT THE FAILED ATTEMPTS OF ATTACKERS WHO THOUGHT THEY WOULD GET LUCKY WITH A BLANK WINDOWS IMAGE. HOW CRAZY. EVEN THEN, WE ARCHITECTED A CLOUD-NATIVE SIEM ENVIRONMENT, AUTHORED CUSTOM KQL QUERIES, IMPLEMENTED THE AZURE MONITORING AGENT, MADE AN ATTACK MAP OUT OF IT, AND SIMULATED A REAL-WORLD SOC WORKFLOW ALL IN ONE DAY. BY FAR, THIS WAS MY FAVORITE LAB AND I HOPE YOU GAINED SOME INSIGHT FROM IT AS WELL. THANK YOU FOR READING.
bottom of page