VULNERABILITY SCANNER DEPLOYMENT
A PROJECT BY DARNELL MAIDEN

INTRODUCTION
ON DECEMBER 9TH, 2021, A VULNERABILITY WAS DISCOVERED THAT ALLOWED USERS IN A MINECRAFT CHAT TO RUN MALICIOUS STRINGS OF CODE THAT WOULD TAKE CONTROL OF A SERVER OR EVEN A COMPUTER FOR THAT MATTER. THAT VULNERABILITY WAS CALLED "LOG4J" ALSO KNOWN AS LOG4SHELL. ALL VERSIONS OF THE MINECRAFT JAVA EDITION WERE VULNERABLE DUE TO JAVA'S LOGGING LIBRARY. TODAY, THE SERVERS TAKE ULTIMATE PRECAUTION, AS LOG4J IS DEEPLY EMBEDDED IN THE SOFTWARE SUPPLY CHAIN.
THE PROBLEM
THESE VULNERABILITIES ARE STILL PREVALENT AND PERSISTENT IN OUR SOCIETY TODAY, CAUSING A HIGH RISK TO PII, SPII, AND OTHER FORMS OF DATA THAT ARE HIGHLY CRITICAL TO OUR EVERY DAY LIVES.
THE SOLUTION
I DEPLOYED AN AUTOMATED VULNERABILITY MANAGEMENT LAB TO PROACTIVELY DISCOVER AND PRIORITIZE NETWORK RISKS. BY UTILIZING ENTERPRISE-GRADE SCANNING TOOLS, I ESTABLISHED A CONTINUOUS MONITORING PIPELINE THAT IDENTIFIES HIGH-IMPACT CVES AND PROVIDES AN ACTIONABLE REMEDIATION ROADMAP TO SECURE CRITICAL DATA.
TECH STACK
ORACLE VIRTUALBOX
WINDOWS 10 ISO IMAGE
NESSUS
STEP 1: PREP
TO START OFF, I SEARCHED FOR A WINDOWS
10 ISO IMAGE ONLINE. I INSTALLED THE "INSTALLATION MEDIA" AND CREATED AN ISO FILE.

ONCE PROMPTED, I CHOSE THE OPTION TO CREATE INSTALLATION MEDIA. THAT'S HOW I GOT MY ISO IMAGE. AFTER GETTING THE ISO IMAGE, I DOWNLOADED VIRTUAL BOX TO MY COMPUTER.

AFTER MY VIRTUAL BOX DOWNLOAD, I PROCEEDED TO UPLOAD THE ISO IMAGE AND MODIFIED SOME PARAMETERS FROM UNATTENDED GUEST INSTALLATION TO THE MEMORY REQUIREMENTS.

NOW, THE UNATTENDED GUEST INSTALLATION IS A MUST BECAUSE IT ALLOWS YOU TO CREATE YOUR USERNAME, PASSWORD, AND YOUR HOST/DOMAIN NAME. I CHECKED OFF GUEST ADDITIONS BECAUSE IT GIVES ME THE COPY/PASTE FUNCTIONALITY.

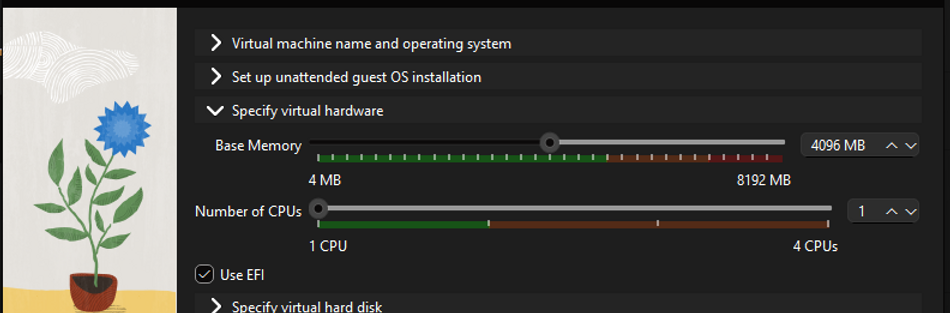
4GB/2 CPUS ARE THE RECOMMENDED SIZE REQUIREMENTS TO MAKE THE VM RUN SMOOTH BUT IF YOU HAVE A BIGGER AND BETTER SYSTEM, I SAY, GO HARD OR GO HOME. AFTER PLUGGING IN MY SETTINGS, IT WAS TIME TO GO TO WORK.
STEP 2: THE BREAKDOWN
AFTER MY VM BOOTED UP, I HAD A PLAN TO MAKE MY SCANNER WORK A BIT HARDER AND MAKE IT WORTH WHILE. IN ORDER TO CATCH A VULNERABILITY, YOU MUST ATTRACT THEM. SO WHAT DID I DO SO SPECIAL?
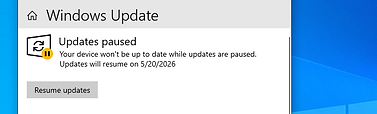
I PAUSED ALL THE UPDATES FOR MORE THAN 7 DAYS, WENT TO THE UPDATE HISTORY, AND UNINSTALLED ANY UPDATES FROM THE LATEST TO THE FIRST. EVERYTHING MUST GO.



THEN I TURNED OFF THE DOMAIN,
PUBLIC, AND PRIVATE FIREWALLS SO THESE VULNERABILITIES CAN HAVE A WELCOME MAT INTO THE TEST VM. I GOTTA BE A GOOD "HOST", YOU KNOW? GET IT? CAUSE... NEVERMIND, KEEP SCROLLING.
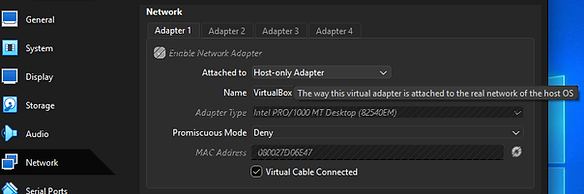
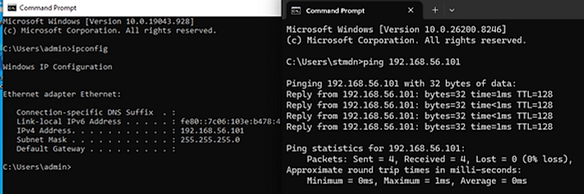
IN ORDER FOR THE VM AND NESSUS TO WORK TOGETHER IN LOVE AND HARMONY, I GOT TO MAKE SURE THEY'RE ON THE SAME NETWORK. I WENT TO MY DEVICE SETTINGS AND CHANGED THE NETWORK TO "HOST ONLY" ADAPTER. TO TEST THIS, I PINGED THE VM FROM MY HOST MACHINE. IT WAS A COMPLETE SUCCESS AND I WAS READY TO SET NESSUS UP.
STEP 3: ENTER THE NESSUS
AFTER CONFIGURING MY SYSTEM AND SETTING IT UP TO BE COMPLETELY RUINED BY EVERY VULNERABILITY POSSIBLE, I WENT TO TENABLE.COM AND GOT MY COPY OF NESSUS. LET ME SHOW YOU HOW THAT WENT.

I WENT TO TENABLE.COM AND SEEN THE WORD "FREE". I IMMEDIATELY JUMPED ON IT LIKE A KANGAROO TO AN OPEN TRAMPOLINE.
GOT MY DOWNLOAD AND ATE RICE WHILE I WAITED. IT WAS BOMB BY THE WAY. NEEDED MORE SALT THOUGH.


WENT THROUGH AN SSL CHECKPOINT AND STILL TOOK THE RISK BECAUSE WHY NOT TENABLE? GO AHEAD AND RISK AWAY.
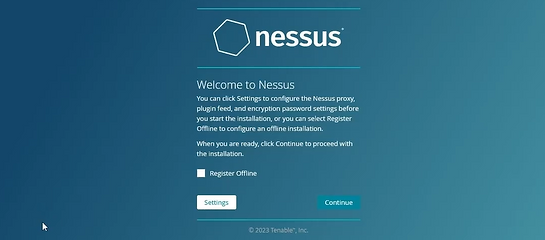
I LANDED HERE, GAVE MY ACTIVATION CODE, CREATED MY CREDENTIALS, AND IT BEGAN DOWNLOADING.
AND AFTER WAITING FOR WHAT FELT LIKE HOURS...

...I WAS IN. TIME TO DO WORK.
STEP 4: EXPLORATION AND EXECUTION

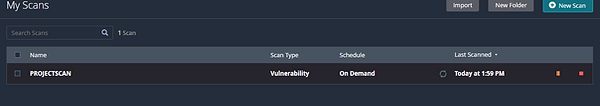
SO MANY OPTIONS. SO MANY SCANS. SO LITTLE TIME (AND MONEY). THIS IS THE "MY SCANS" SECTION. LET'S GO THROUGH A FEW AND GET ACQUAINTED.
"BASIC SCAN" IS AN OPTION THAT SCANS FOR OPEN PORTS, RUNNING SERVICES, AND UNDERSTANDING THE SECURITY POSTURE OF YOUR NETWORK PLUS POTENTIAL VULNERABILITIES.
"MALWARE SCAN" IS DESIGNED TO HELP YOU IDENTIFY MALWARE THAT MAY BE PRESENT ON THE SYSTEM. RUNNING THIS SCAN CAN HELP YOU DETECT AND REMOVE MALWARE FROM YOUR NETWORK.

"ACTIVE DIRECTORY (AD) SCAN" IS DESIGNED TO ASSESS THE SECURITY POSTURE OF DOMAIN CONTROLLERS. IT IDENTIFIES MISCONFIGURATIONS, VULNERABILITIES, AND WEAKNESSES IN AD SERVICES-SPECIFICALLY LDAP, KERBEROS, AND SMB-THAT ATTACKERS EXPLOIT TO STEAL CREDENTIALS, ESCALATE PRIVILEGES, AND MOVE LATERALLY.
NOW THAT WE GOT OUR PLEASANTRIES OUT OF THE WAY WITH A FEW OF THE VARIATIONS, LET'S CREATE A NEW SCAN. I HAD TO INPUT THE A NAME FOR IT ALONG WITH THE TARGET IP ADDRESS. TO VERIFY, I WENT TO MY COMMAND PROMPT IN MY VM AND RAN THE <IPCONFIG> COMMAND JUST SO I CAN GET THE RIGHT IP.


DID YOU KNOW THAT NESSUS OFFERS THE ABILITY TO SCHEDULE PERIODIC SCANS? IF YOU ENABLE THIS YOU CAN RECIEVE NOTIFICATIONS VIA EMAIL. VERY CONVIENIENT.

LET'S BREAK DOWN MORE SECTIONS FOR PROPER CLARIFICATION.

IN THE DISCOVERY SECTION, YOU CAN CHANGE THE SCAN TYPE TO COMMAND PORTS, ALL PORTS, OR CUSTOM. IF YOU CHOOSE THE CUSTOM OPTION, YOU WILL HAVE EVEN MORE OPTIONS AVAILABLE FOR HOST DISCOVERY, FOR SCANNING PORTS, SERVICE DISCOVERY. AND IDENTITY.
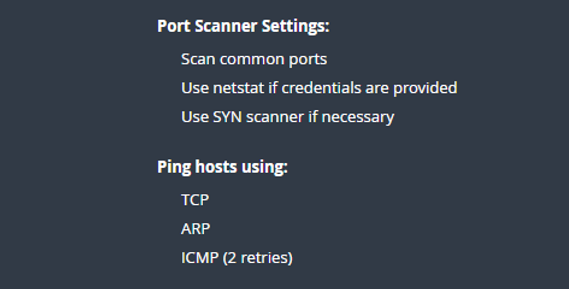
THE PORT SCAN (COMMON PORTS) OPTION WILL PING HOSTS USING TCP, ARP, AND ICMP. IT WILL ALSO USE A SYN SCANNER WHICH SCANS FOR THE MORE COMMON PORTS SUCH AS FTP, SSH, TELNET, SMTP, AND MUCH MORE.

THE ASSESSMENT SETTINGS ALLOW YOU TO CONFIGURE HOW THE SCANNER PERFORMS THE SCAN AND WHAT TYPE OF VULNERABILITIES IT LOOK FOR. THERE ARE TWO CATEGORIES OF ASSESSMENT SETTINGS, GENERAL SETTINGS AND WEB APPLICATION SETTINGS.

UNDER GENERAL SETTINGS, THERE ARE TWO OPTIONS: AVOID POTENTIAL FALSE ALARMS, WHICH INSTRUCTS THE SCANNER TO SKIP CERTAIN CHECKS THAT MAY PRODUCE FALSE POSITIVES. IT CAN REDUCE THE NUMBER OF ALERTS BUT CAN MISS LEGITIMATE VULNERABILITIES. THE SECOND OPTION IS TO DISABLE CGI SCANNING, WHICH TURNS OFF COMMON GATEWAY INTERFACE CGI SCRIPTS. IF YOU TURN THIS OFF, YOU CAN MISS LEGITIMATE VULNERABILITIES.
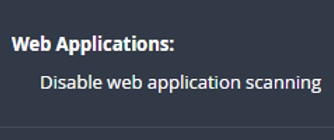
UNDER THE WEB APPLICATION SETTINGS, YOU CAN DISABLE WEB APPLICATION SCANNING. IT WILL STOP THIS SCANNER FROM LOOKING FOR VULNERABILITIES IN WEB APPLICATIONS ALTOGETHER. WEB APPLICATIONS ARE DEFINITELY A TARGET FOR ATTACKERS AND VULNERABILITIES IN WEB APPLICATIONS THAT CAN BE EXPLOITED TO GAIN ACCESS TO SENSITIVE DATA OR COMPROMISE THE SERVER.

NOW WE MOVE TO "REPORTS" SECTION. HERE, YOU CAN CONTROL HOW THESE SCAN RESULTS ARE PROCESSED AND PRESENTED TO THE USER. YOU HAVE THE OPTION TO ADJUST THE LEVEL OF DETAIL TO YOUR SPECIFIC NEEDS AND REQUIREMENTS.
IN THE ADVANCED SETTINGS, YOU CAN CONTROL THE NUMBER OF HOSTS THAT WILL BE SCANNED AT THE SAME TIME WHEN THE NETWORK READS TIME OUT.

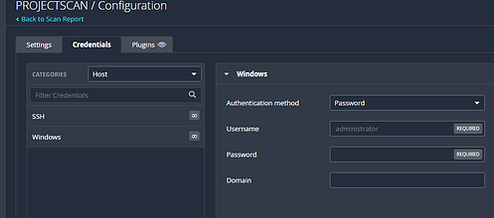
YOU CAN ALSO PROVIDE NESSUS WITH CREDENTIALS. PERFORMING A CREDENTIAL SCAN WITH NESSUS CAN PROVIDE SEVERAL ADVANTAGES OVER A NON-CREDENTIAL SCAN INCLUDING INFORMATION ABOUT INSTALLED SOFTWARE PAGE LEVELS AND SYSTEM CONFIGURATIONS THAT MIGHT BE CRITICAL FOR DETECTING VULNERABILITIES AND RISK.
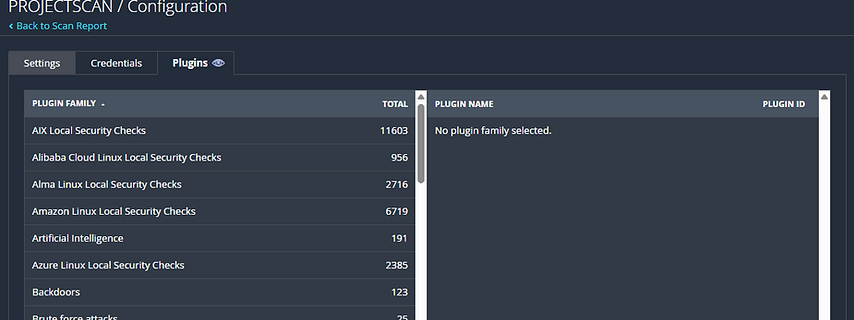
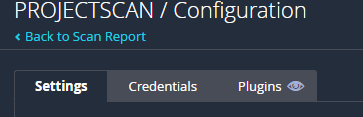
LASTLY, THERE ARE THE PLUGINS. THESE PLUGINS ARE ORGANIZED INTO FAMILIES BASED ON THEIR FUNCTION OR THE TYPE OF VULNERABILITY THEY TARGET.
STEP 5: SCANNING AND PLANNING
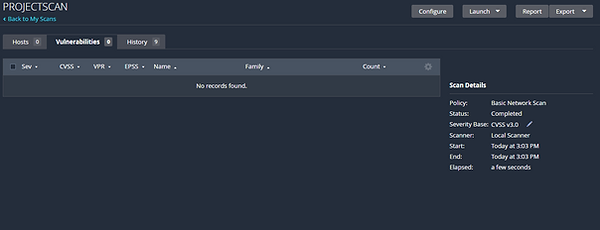
ALRIGHT, SO AFTER HITTING THE LAUNCH BUTTON AND WAITING FOR ABOUT 30 MINS, I CLICKED ON MY SCANNER AND FOUND THIS....

SO LET'S LOOK AT THAT BOTTOM RIGHT SECTION.
THIS GRAPH CLASSIFIES EVERY VULNVERABILITY INTO 5 DIFFERENT LEVELS. CRITICAL, HIGH, MEDIUM, LOW, AND INFO. THIS HELPS WHEN YOU NEED TO IDENTIFY THE MOST IMPORTANT VULNERABILITIES THAT REQUIRE IMMEDIATE ATTENTION.


THE VULNERABILITY TAB GIVES DEEPER INFORMATION ABOUT THE VULNERABILITIES AT HAND IN AN ORGANIZED AND READABLE FORMAT.
ONE FINDING INFORMED ME THAT THE REMOTE HOST IS LISTENING ON DP PORT 137 OR TCP PORT 445. CYBER CRIMINALS OFTEN EXPLOIT VULNERABILITIES ON PORT 445 TO SPREAD "WANNACRY" RANSOMWARE. YOU CAN USE THIS INFO TO PROTECT YOUR NETWORK AND PREVENT SECURITY BREACHES.


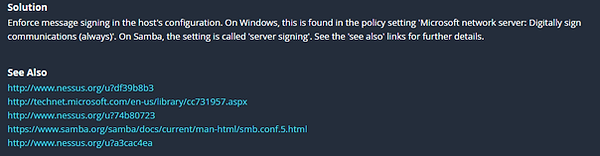
LET'S LOOK AT ANOTHER ONE. THIS ALERT SAYS SMB SIGNING NOT REQUIRED. AN UNAUTHENTICATED REMOTE ATTACKER COULD EXPLOIT THIS AND CONDUCT A MAN IN THE MIDDLE ATTACK WHICH IS WHEN AN ATTACKER INTERCEPTS A CONNECETION BETWEEN TWO PARTIES TO GET SENSITIVE INFORMATION.
NESSUS PROVIDES YOU WITH A SOLUTION AS WELL AS URL RESOURCES FOR MORE INFORMATION ON THE VULNERABILITY, THE CAUSES, AND EVEN WAYS TO PREVENT IT.
STEP 6: EXTRA CRED...ENTIALS.
NOW, WE'RE GOING TO ADD CREDENTIALS TO OUR SCAN TO GET MORE INFORMATION
LET'S NAVIGATE TO THE "MY SCANS" SECTION AND SELECT THE SCAN I'M WORKING ON. (PROJECTSCAN).
AFTER THAT I HEADED TO THE TOP RIGHT AND CLICK
"CONFIGURE" > "CREDENTIALS"
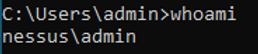
THE VIRTUAL MACHINE I'M WORKING WITH IS WINDOWS BASED SO OBVIOUSLY I'LL SELECT WINDOWS. THERE ARE SEVERAL AUTHENTICATION METHODS THAT CAN BE USED. THE AVAILABLE OPTIONS ARE PASSWORD, KERBEROS, LM HASH, AND NTLM HASH. I CHOSE THE PASSWORD OPTION AND FILLED OUT THE NECESSARY INFO. IF YOU FORGET YOUR DOMAIN NAME, TYPE 'WHOAMI' IN THE COMMAND PROMPT.

AFTER THAT PROCESS WAS DONE, I RECIEVED A NOTIFICATION ABOUT THE ACCOUNT NOT HAVING THE NECESSARY PRIVILEGES TO RUN THE SCAN.


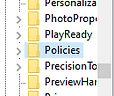
TO FIX THIS, I WENT BACK TO MY WINDOWS VIRTUAL MACHINE AND SEARCHED FOR "SERVICES" > "REMOTE REGISTRY".
I NAVIGATED TO REMOTE REGISTRY NEXT AND CHANGED THE STARTUP TIME TO AUTOMATIC. THIS WILL ALLOW ME TO AUTOMATICALLY CONNECT TO THE SYSTEM REGISTRY DATABASE AND PERFORM DIFFERENT OPERATIONS SUCH AS VIEWING REGISTRY KEYS AND VALUES.
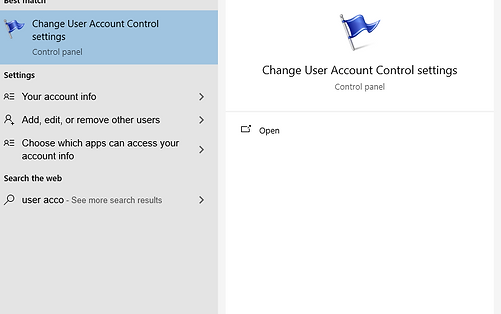
I SLID THE BAR TO THE BOTTOM TO NEVER NOTIFY. THIS WILL PREVENT USER ACCOUNT CONTROL PROMPTS FROM INTERRUPTING THE SCAN.




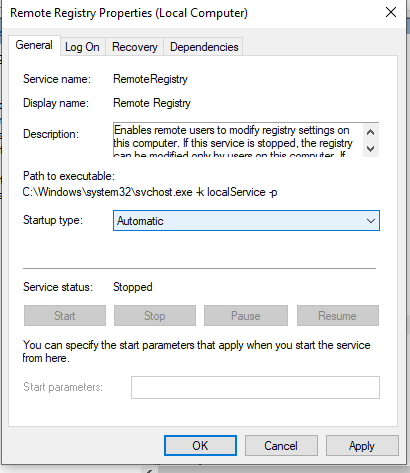
ONCE I GOT TO THE "SYSTEM" FOLDER, I CREATED A "DWORD (32-BIT) VALUE. THIS WILL CREATE A NEW REGISTRY VALUE. JUST SO I COULD FIND IT FASTER, I NAMED IT "LOCAL ACCOUNT TOKEN FILTER POLICY".
NEXT, I SEARCHED FOR THE USER ACCOUNT CONTROL OPTION.


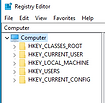
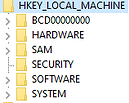
LASTLY, I OPENED THE REGISTRY EDITOR AND NAVIGATED IN THIS ORDER TO CREATE A NEW VALUE.
HKEY LOCAL MACHINE>SOFTWARE>MICROSOFT>WINDOWS>CURRENT VERSION>POLICIES>SYSTEM
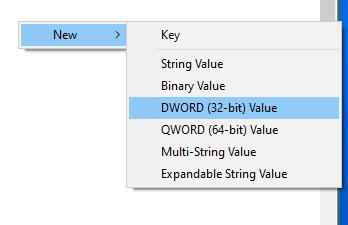
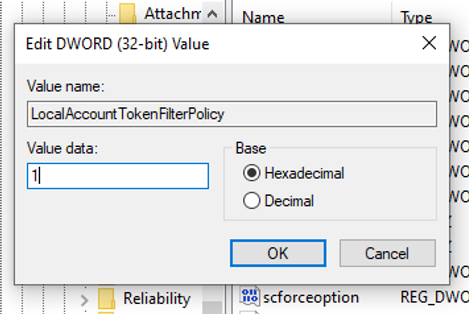
I DOUBLE-CLICKED THE VALUE TO EDIT IT'S PROPERTIES. I NEED TO TURN IT ON SO I CHANGED THE VALUE DATA FIELD FROM 0 TO 1. THIS WILL ENABLE THE LOCAL ACCOUNT TOKEN FILTER POLICY WHICH ALLOWS NON-ADMIN ACCOUNTS TO ACCESS ADMINISTRATIVE RESOURCES ON THE SYSTEM AND USING REMOTE PROCEDURE CALL. AFTER THIS I RESET MY VM.
STEP 7: SCAN WITH THE PLAN
ALRIGHT, TIME TO LAUNCH ANOTHER SCAN. IM SURE IT'S GOING TO BE... OH...

WELL THEN... TIME FOR SOME FURTHER ANALYSIS. THIS IS EXACTLY WHAT I WANTED. LET'S GO.
STEP 8: UP THE STAKES
OH MAN, SO MANY VULNERABILITIES, SO LITTLE TIME. LET'S ADD MORE, BUT FIRST, LET'S CHANGE THE ADAPTER SETTINGS. I HEADED TO DEVICES>NETWORK>NETWORK SETTINGS AND I CHANGED IT FROM HOST-ONLY TO BRIDGED ADAPTER. NOW WE'RE CONNECTED TO THE INTERNET TO DEPLOY SOME BAD SOFTWARE ON OUR TEST VM.




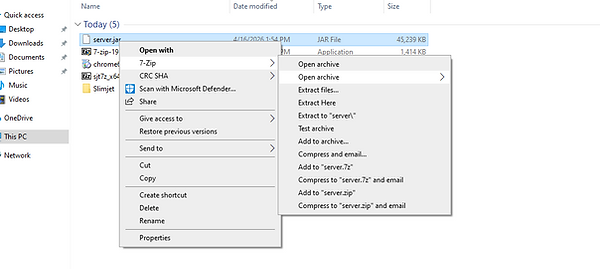
HMMMM.... LET'S DOWNLOAD AN OLD VERSION OF GOOGLE CHROME I HEADED TO SLIMJET.COM BECAUSE WITH AN OUTDATED BROWSER IT MAKES IT EASIER FOR HACKERS TO GET INTO OUR STORED PASSWORDS.
ALSO, TO MAKE IT SWEETER FOR ATTACKERS, I TURNED OFF THE UPDATES FOR THE BROWSER THEN RESET MY VM. BUT WAIT, THERE'S MORE! I DOWNLOADED A MINECRAFT SERVER FILE, BUT I DON'T WANT TO MINE FOR DIAMONDS, I WANT TO VISIT THE HOME OF THE VULNERABILITY I SPOKE ABOUT IN THE BEGINNING, "LOGJ4". LET'S GO KNOCK ON THE DOOR.

AFTER DOWNLOADING THE SERVER FILES, I DECIDED TO DO ANOTTHER SCAN OF MY VM.
STEP 9: VULNERABILITES GONE WILD.
AFTER DOWNLOADING AN OUTDATED MINECRAFT SERVER AND AN OUTDATED GOOGLE CHROME APPLICATION, I RAN THE SCAN ANOTHER TIME...
OH LOOK! THE VULNERABILITY I'VE BEEN SEARCHING FOR! APACHE LOG4J! IT HAS A REMOTE CODE EXECTUTION VULNERABILITY THAT HAS A CVSS CODE OF 10! WE'RE GETTING SOMEWHERE.

LOG4J (OR LOG4SHELL) IS A CRITICAL VULNERABILITY IN THE JAVA-BASED LOGGING LIBRARY THAT ALLOWS AN ATTACKER TO EXECUTE MALICIOUS CODE ON A SYSTEM REMOTELY. BY SENDING A SPECIFIC STRING OF TEXT TO A SERVER, THE ATTACKER CAN TRIGGER A REMOTE CODE EXECUTION (RCE), EFFECTIVELY TAKING COMPLETE CONTROL OF THE TARGET COMPUTER OR SERVER.
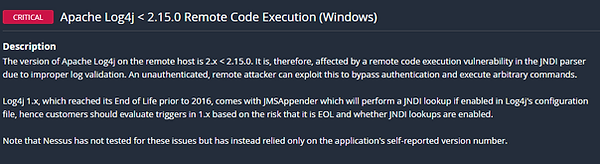
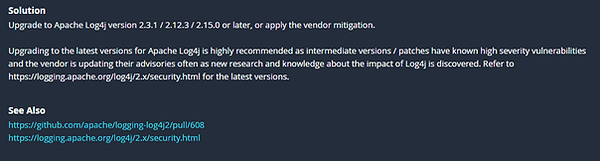
NOT ONLY DOES NESSUS DETECT THE VULNERABILITIES, IT GIVES A BRIEF DESCRIPTION OF IT AS WELL WITH SOLUTIONS AND LINKS WITH FURTHER INFORMATION ON HOW YOU CAN PREVENT THIS VULNERABILITY. THIS CAN HELPFUL FOR STRENGTHENING YOUR SECURITY POSTURE IN FUTURE ENDEAVORS.
NOW WHAT IF I NEEDED TO PINPOINT WHERE IT WAS ON MY OS FOR REMEDIATION? NESSUS HAS A SECTION WHERE YOU CAN SEE THE PATH OF THE VULNERABILITY AND WHERE TO FIND IT AS WELL. THIS IS HELPFUL FOR QUICKER REMEDIATION AND ANALYSIS.
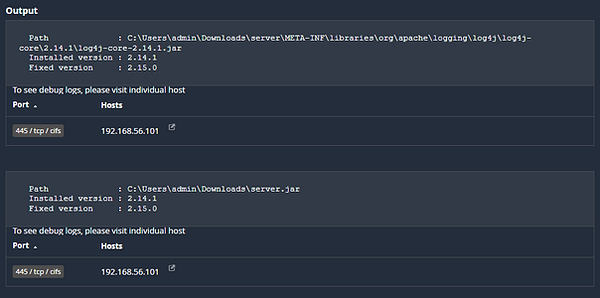
YOU CAN ALSO SEE THE VULNERABILITY/RISK INFORMATION OVERVIEW FOR QUICKER ANALYSIS.


WE CAN'T FORGET ABOUT OUR GOOGLE CHROME APPLICATION. IT HAS SCORES ACROSS THE BOARD WITH A 9.8.



IF WE CLICK ON ONE OF THEM, WE CAN SEE THAT IT CAPTURED MULTIPLE VULNERABILITIES SUCH AS USE AFTER FREE IN PASSWORDS, OUT OF BOUNDS MEMORY ACCESS IN WEB HID, USE AFTER FREE IN PDF, USE AFTER FREE IN ANGLE, AND SO MUCH MORE. I CLICKED ON ANOTHER VULNERABILITY AND DISCOVERED A VULNERABILITY WHERE CRAFTED HTML PAGES COULD POTENTIALLY BE EXPLOITED. THE BEST RECOMMENDATION AT THIS POINT IS TO GRAB THE CVE NUMBER AND DO EXTENSIVE RESEARCH. SOLUTIONS AND LINKS ARE PORVIDED AS WELL.
STEP 10: CLEANING HOUSE
NOW LET'S FIX THE ISSUES WE'VE CREATED. I'LL PROCEED WITH REMEDIATION BY RESUMING THE UPDATES FIRST.


NEXT, WE'LL UPDATE GOOGLE CHROME.

LASTLY, I WENT TO THE DOWNLOADS FOLDER AND REMOVED THE MALICIOUS SERVER FILES FROM MINECRAFT THEN EMPTIED THE RECYLING BIN.


AND ONCE WE DO ANOTHER SCAN....